
Turn It Off Or Fix It.
Millions of Scammers are About to Get a Brand New Weapon
Your website is the weapon.
Your customers are the victims.
Scamming is a trillion-dollar-a-year industry. Five million professionals. Phone scams. Email scams. Romance scams. Call centres. Scripts. A boss who takes 80-90% of the money.
They haven’t discovered AI hacking yet. But the tutorials are on YouTube. Right now. Free. Public.
When word spreads through a trillion-dollar criminal industry that they can ditch the call centre, keep every dollar, and hack websites from their lounge room with a laptop and a jailbroken AI — you’ll know. Everyone will know. The volume of attacks will go from thousands to millions overnight.
That wave hasn’t hit yet. But it’s coming. Within 12 months.
When it does, Google flags your site. Chrome throws a full-screen red warning — “Deceptive Site Ahead.” Your Google Ads get suspended. Your phone stops ringing. Not slowly. Overnight.
You have two options: turn your website off or protect it. There is no third option.
Running a website without due diligence isn’t just risky — it’s negligent.



The Attack Nobody's
Warning you About
Here’s what your ‘web guy’ doesn’t know: The threat isn’t data theft. The threat is that YOUR WEBSITE becomes the weapon — and your customer’s entire computer becomes someone else’s property.
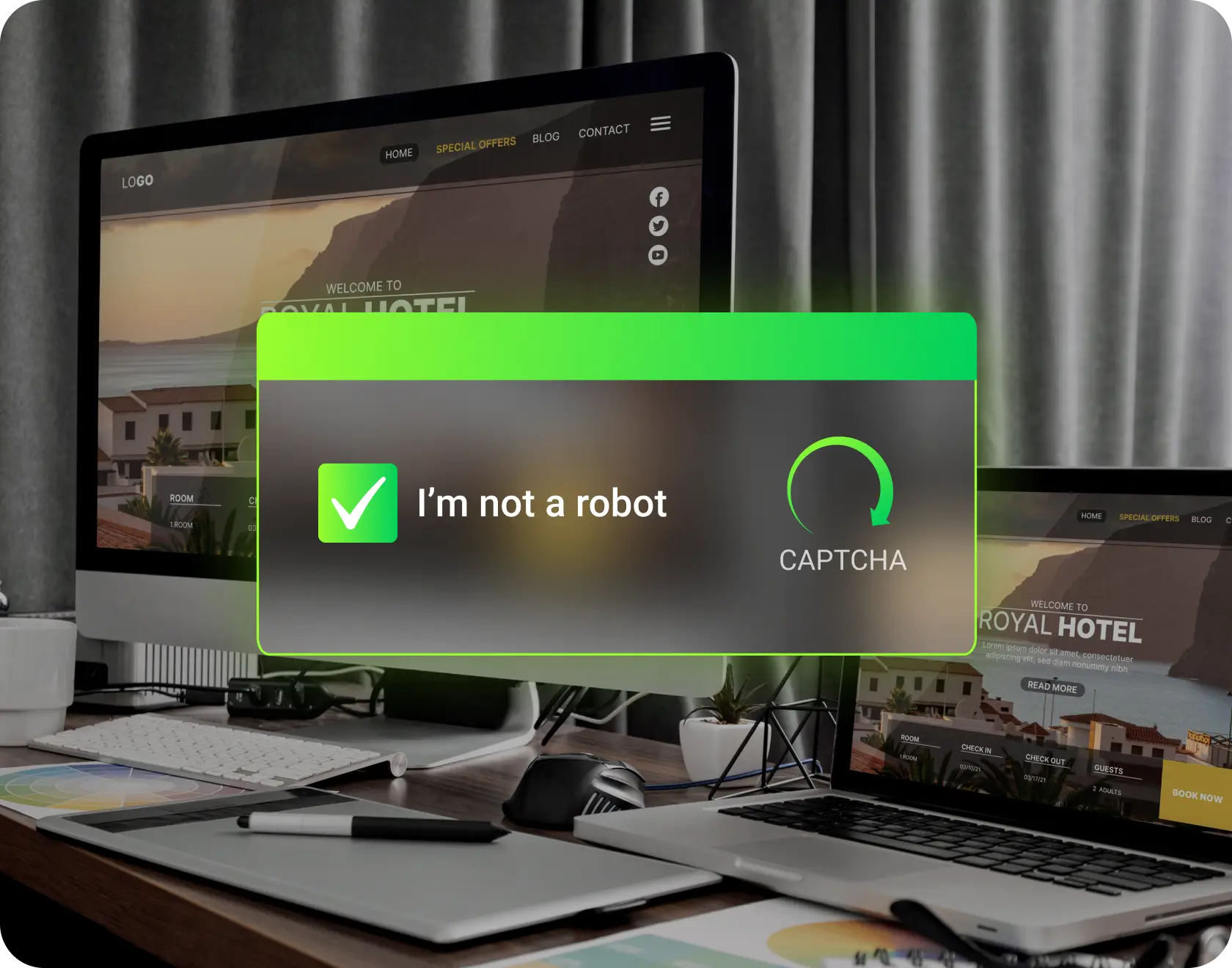
Picture this: A customer visits your site. Instead of your homepage, they see a Cloudflare ‘Verify you’re human’ CAPTCHA. Looks completely legitimate. They click it.
Instantly — no download prompt, no warning — malware installs on their computer.
But this isn’t the smash-and-grab you’re imagining. Nobody steals a credit card number and runs. That’s yesterday’s threat.
What happens next is full machine takeover. For weeks. Sometimes months.
Sleep code activates. A persistent backdoor opens. Someone is now living inside your customer’s computer. Not metaphorically. Literally. They have a terminal session. They can see the screen. They record everything. Every keystroke. Every banking session. Every private message. Every document opened.
The attacker gets a notification: ‘New backdoor active.’ Then they settle in.
They watch. They wait. They harvest. They don’t rush — because nobody knows they’re there.
The Victim's Anti Virus?
It sees Nothing.
We’ve tested this. Over 95% of mainstream security software completely missed it. The malware looked like normal web traffic — rotating proxies, encrypted payloads, nothing to flag.
Your customers’ antivirus won’t catch it. Their firewall won’t block it. The only thing standing between your website and their devices is you.
That’s what Website Rescue does — we keep your site monitored and hardened so threats get caught early, and if something does slip through, we detect it fast and notify you before it becomes your liability.

You Think You’re Too
Small to Target
You run a local business. Maybe 50 customers a month visit your site. Why would anyone bother hacking you?
Here’s why that logic is dead.
Automated bots scan 36,000 websites per second. They’re not looking for valuable targets — they’re looking for vulnerable ones. They don’t read your About page. They don’t check your revenue. They run a script that tests your WordPress version, your plugin list, and your server configuration. If something’s exploitable, you’re in.
You’re not being targeted. You’re being swept. Like a trawler net dragging across the ocean floor. The fish aren’t chosen — they’re just there when the net passes.
Think of it like car break-ins. Thieves don’t target expensive cars — they target unlocked ones. Your website is an unlocked car sitting on a street that 36,000 thieves drive down every second.
And here’s what makes it worse: small businesses are actually better targets. You don’t have a security team. You don’t have monitoring. You probably won’t notice you’ve been compromised for weeks or months. That’s exactly what attackers want — a quiet host where they can set up shop, install sleep code, and use your site to infect every visitor who trusts you.
The attack on your customers won’t come from a suspicious Russian domain. It’ll come from your domain. Your trusted brand. That’s the whole point.

Your “Web Guy” Doesn’t Know
This Threat Exists
You have someone who handles your website. Maybe a freelancer, maybe an agency, maybe your nephew who’s “good with computers.” They built you a solid site. It looks professional. It works.
But here’s what they’re not doing: tracking zero-day exploits, monitoring dark web forums for new attack vectors, or reading security advisories from WordPress plugin developers.
Why? Because that’s not their job.
Your web developer is hired to build and maintain a website. They’re skilled at design, user experience, maybe SEO. They update plugins when WordPress nags them. They might even run backups.
But cybersecurity? Threat intelligence? Jailbroken AI exploits that emerged three months ago? The workforce transition that’s about to flood the market with millions of new attackers? That’s a completely different discipline. It’s like expecting your accountant to also be your lawyer. Same office, completely different expertise.
The uncomfortable truth is this: your site can be beautifully designed, professionally maintained, running the latest WordPress version — and still be completely vulnerable. Updated does not equal secure. Because the attacks aren’t targeting your code. They’re targeting your plugins, your server, your hosting configuration, your admin password policy. Things your web guy never thought to check because nobody asked them to.
This isn’t their fault. It’s a gap in the system. And a trillion-dollar criminal industry is about to discover it.

Your Obscurity Was Your Shield.
That’s Gone.
Hackers used to go after big targets. Banks. Governments. Corporations. Why waste time on a local tradie’s website when you could hit Optus?
Hacking required skill. Skill costs money. Big targets justified big investments.
AI flipped that equation.
Automated bots now scan 36,000 websites per second. They don’t choose targets — they sweep everything. Like a trawler net dragging across the ocean floor. The fish aren’t chosen — they’re just there when the net passes.
Scamming is already a trillion-dollar-a-year industry. Five million professionals who haven’t discovered AI hacking yet. When they do — and the tutorials are sitting on YouTube waiting for them — every one of them ditches the call centre, keeps every dollar, and works from home. The volume of attacks goes from thousands to millions.
Old model: Find valuable targets → Invest time → Attack carefully
New model: Attack everything → See what works → Exploit winners
Your obscurity — the fact that nobody knows your business exists — used to protect you. Now it just means you won’t see it coming.
And when they get in, Google finds out before you do. Chrome slaps a full-screen red “Deceptive Site Ahead” warning on your URL. If you’re running Google Ads — the thing that actually makes your phone ring — Google suspends your account the moment they detect malware. No warning. No grace period. Suspended.
Big companies have security teams watching for attacks. You have… hope?
When the cost of attack is zero and the workforce is unlimited, everyone is a target. Size doesn’t matter anymore. Only vulnerability matters. 
Set and Forget
No Longer Works
For the past 15 years, small business websites basically ran themselves. You’d pay someone to build it, maybe update it once a year, and forget about it. If something broke, you’d notice — the site would go down, or the contact form would stop working.
That era is over.
Modern attacks don’t break your site. They don’t crash it. They don’t deface it with skulls and political messages. That’s amateur hour.
Professional attacks are silent. They inject sleep code — malicious code that sits dormant until a visitor arrives. They create invisible redirects. They install persistent backdoors that survive even if you restore from backup. They add themselves to your scheduled tasks so they reinstall every night at 3am.
Your site looks fine. It works fine. You have no idea anything’s wrong — until a customer discovers someone has been living inside their computer for three weeks. Recording their screen. Logging every password. Watching every banking session. All because they visited your website and clicked something that looked completely normal.
The old model was: if nothing looks broken, nothing is broken.
The new reality is: the most dangerous infections are the ones you can’t see.
A neglected website isn’t sitting there doing nothing. It’s a loaded weapon pointed at everyone who trusts you enough to visit.

You Can’t Outsource
This Decision
Here’s what usually happens: business owner hears about website security, thinks “I should look into that,” then gets busy and forgets. Or they ask their web guy, who says “yeah it’s fine, I updated the plugins last month.” And that’s where it sits. In the “someday” pile. Between “redo the logo” and “fix the About page.”
But here’s the thing about security: it’s not a website task. It’s a business decision. And business decisions don’t belong to your web guy, your hosting company, or that mate who “knows computers.”
Your hosting company secures their servers. Not your WordPress installation.
Your web developer builds features. They’re not watching for new exploits.
Your antivirus protects your computer. Not your visitors’ computers when they land on your infected site.
There’s a gap between all these people. And your business is sitting in that gap, unprotected.
The only person who can close that gap is you. Not by becoming a security expert — that’s our job. But by deciding that it matters. By putting it on the agenda. By getting it checked, documented, and handled.
Nobody else is going to do this for you. Everyone assumes someone else is handling it.
That’s exactly why most small business websites are vulnerable — not because the owners don’t care, but because they assumed it was already covered.
It’s not. And now you know.
How AI Attacks Everything At Once
When a jailbroken AI is pointed at your business, it doesn’t try one thing at a time. It attacks EVERY surface simultaneously:
01
Your WordPress admin login — Credential stuffing with millions of stolen passwords
02
Every plugin you’ve installed — Each one is a potential backdoor
03
Your hosting control panel — cPanel, Plesk, whatever you’re running
04
Your contact forms — Injection points for malicious code
05
Your database connection — SQL injection to access everything
06
Your file upload fields — Direct malware insertion
07
Your theme files — Hidden code in templates you never check
08
Your scheduled tasks — Persistence mechanisms that survive cleanup
09
Your DNS settings — Redirecting your entire site to their servers
A human hacker picks one angle and works it. AI doesn’t have that limitation. It tries everything. At once. In parallel. Across thousands of sites simultaneously. And it only needs ONE thing to work. Human attackers get tired. AI doesn’t. Human attackers cost money. AI is free. Human attackers move on to easier targets. AI has infinite patience — it’ll keep trying your site while it attacks a million others.
What They're
Really After
Forget the old ‘hackers want your credit card number’ narrative. That was smash-and-grab. Today’s AI-powered attacks are playing a longer, darker game:

Full Machine
Occupation
They don’t steal one thing and leave. They move in. Sleep code activates a persistent backdoor — a live terminal session inside your customer’s computer. Someone is sitting there, watching their screen in real time, for weeks. They see every document opened. Every email sent. Every private conversation. The victim has no idea anyone’s there.
Every password typed. Every banking session recorded. Every login to every service — work email, personal email, cloud storage, accounting software, social media. One infection gives the attacker keys to the victim’s entire digital life. Not one account. All of them.
Digital Asset
Extraction
Crypto wallets. Banking codes. Investment accounts. Saved payment methods. AI uses OCR to extract seed phrases from screenshots. Clipboard monitoring catches wallet addresses mid-transaction. Life savings, gone — and the victim won’t know for weeks because the attacker is patient.
The backdoor runs scheduled sweeps — scanning your customer’s machine weekly for new assets. New browser-saved passwords. New banking sessions. New crypto wallets installed. Every keystroke is filtered for card numbers, BSBs, login credentials, and recovery phrases. It’s not a one-time grab — it’s an ongoing harvest that gets more valuable the longer it sits undetected.
Persistence
& Resale
When the attacker has squeezed everything they can, they don’t close the backdoor. They sell access to the next attacker. Your customer’s computer becomes a commodity — traded on dark web marketplaces. Machine access sold for $5–$50. Multiply that by every visitor your site infects.
This isn’t hypothetical. Microsoft discovered StilachiRAT — a trojan that specifically targets 20 different cryptocurrency wallet browser extensions, extracts saved credentials, monitors clipboard for wallet addresses, and exfiltrates everything to attackers. And that’s just one they caught.
The ones they haven’t caught are the ones already sitting on your customers’ machines. Watching. Recording. Waiting.
Your 3-Step Website
Rescue Plan
How We Protect You
01
Free Scan →
Full Discovery
It starts with a free external scan — we probe your site the way an attacker would, from the outside. You’ll see what’s exposed without us needing access to anything.
Our scanner is built from scratch — not a resold plugin or a generic tool. It checks your WordPress version, PHP version, plugin list, theme vulnerabilities, SSL config, header security, and known exploit paths. Every finding is cross-referenced against the WordPress vulnerability database and Wordfence threat intelligence feed in real time.
We’re honest: because we stay on the right side of the line, version numbers and configs detected externally aren’t always exact. But we’re usually pretty close — and even the external view catches things most site owners had no idea were visible.
The full picture comes with Discovery. You give us logins, we go inside — plugins, configs, server settings, the stuff no external scan can see. That’s where the real gaps show up. We stop at the white hat line. We find the problems. You see the full truth about your site.
02
Hardening +
Remediation
Most sites we assess need work — even ones that look “up to date.” Updated plugins aren’t the same as secure plugins. Some of the most popular WordPress plugins have known vulnerabilities that updates alone don’t fix.
The longer a site’s been running without a security review, the more entry points have quietly stacked up.
We harden in staging first — never on your live site. Firewall rules tightened. Risky plugins replaced or locked down. Login security layered. File permissions corrected. PHP version checked. Database access restricted. Admin paths hidden from bots. Scheduled tasks audited for persistence code.
Every change tested before it touches production.
03
Certification +
Monitoring
Your Certificate of Due Diligence proves you acted — not hoped, not guessed, acted. A live verification badge on your site that anyone can click to confirm your protection status in real time.
Behind it: 24/7, 365-days-a-year automated monitoring with instant alerts if anything changes. Plus a real person checking your site every week — eyes on your plugins, your core, your server config. Not a bot. A human who knows what to look for.
When something moves, we see it and we act before your customers pay the price.
And here’s the bonus you don’t expect: because we’re already inside your site every week checking security, all the maintenance happens as a byproduct. Plugin updates. PHP upgrades. Broken features caught early. Performance issues spotted before your customers notice.
You’re not just getting security — you’re getting a maintained website without paying a separate web guy to do it.

The Legal Reality
Nobody Mentions
When a customer gets infected through your website, their lawyer subpoenas your hosting logs.
Everything is timestamped. When you last updated your plugins. Whether you’ve ever run a security audit. How long the infection was active before you noticed — if you noticed at all.
You either didn’t know your site was infected — meaning zero monitoring, zero due diligence — or you did know and stayed quiet, hoping nobody would trace it back to you.
Either way, that’s negligence. Provable, documented, timestamped negligence.

Without Certification:
The Impossible Position
When your site becomes a malware distribution point and you don’t have a care plan:
If you warn users: You’re admitting you were the source. Everyone knows who to sue.
If you stay silent: That’s negligence. When discovered, your position is worse.
You’re trapped either way.
A lawyer subpoenas your hosting logs. Everything is timestamped — when you last updated, whether you ever ran a security audit, how long the infection was active. Provable, documented, timestamped negligence.
No security audit on file. No update schedule. No monitoring. No incident response plan. The court doesn’t need to prove you were careless — your own server logs do it for them.
Your insurance won’t cover it if you can’t demonstrate you took reasonable steps to prevent it. Most standard business policies exclude cyber negligence.
This isn’t hypothetical. Australian businesses face mandatory breach notification under the Privacy Act 1988. If personal data was exposed through your site, you’re legally required to report it — and explain what safeguards you had in place.
With Our Certificate:
The Story Changes
With Website Rescue certification, the story flips completely:
Monitoring catches it fast. Our systems detect changes within hours, not months. We patch in staging, test thoroughly, and push live — before damage spreads.
Detection flags threats immediately — not weeks or months later. While most businesses discover breaches from their customers or Google, yours gets caught at the source.
Pre-prepared notification to your customers within hours. We’ve already drafted the response template, so you’re not scrambling to figure out what to say while the clock is ticking.
Certificate of Due Diligence — documented, timestamped proof that you were actively monitoring, updating, and maintaining your website security. The one document that changes everything in court.
Timestamped evidence: every update logged, every scan recorded, quarterly security reports on file. Your lawyer doesn’t have to argue you were careful — they can prove it.
Their lawyer advises them to drop it. When they see the documentation, the monitoring logs, the incident response — there’s nothing to win here. You did everything right.
That’s the difference between a lawsuit you lose and a lawsuit that never gets filed.
Your insurance stays valid because you can prove due diligence. Documented updates, monitored 24/7, incident response in place.

What We Actually Do
(The Technical Reality)
Website Rescue isn’t cybersecurity. We don’t reverse-engineer malware or track nation-state actors. That’s enterprise territory with six-figure budgets.
We do something different: We make sure YOU’RE not the one everyone points at when things go wrong.

We’re there making sure your security is right — and most of your maintenance is part of that:
Site hardening — your site gets locked down properly from day one
Firewall configuration — enterprise-grade protection tuned to your setup
Login security — hidden admin URLs, geo-blocking, 2FA, brute-force lockout
Plugin and theme updates — an outdated plugin is a security hole, so everything stays current
PHP and database updates — the stuff nobody thinks about until it breaks
Vulnerability audits — every plugin checked, risky ones removed or replaced
Staging environment — all changes tested before they touch your live site
Code execution controls — only approved code runs, nothing injected
Real-time monitoring — if something changes, we know about it before you do
Incident response — detection triggers an immediate alert and action
It doesn’t cover everything — but it covers most of it.
Honest Positioning: We can never make your site 100% hack-proof. Nobody can. Anyone who promises that is lying.
But we CAN make sure you’re not neglecting your responsibility to your website users — and we CAN give you the documentation to prove it.

Ready to Stop Being a
Sitting Duck
Certificate of Due Diligence with ongoing protection plans
The wave is coming. Five million professional scammers are about to discover AI hacking. The tutorials are already on YouTube. You have maybe 12 months before attack volumes go from thousands to millions.
You don’t need to panic. But you need to stop guessing. When a customer’s lawyer subpoenas your hosting logs, “I didn’t know” isn’t a defence — it’s proof of negligence.
Find out what’s on your site. Free. Right now.
